Exploring the Integration of Cybersecurity in Tourism: A Guide to Legal Private Hacker Contact Methods and Safety Protocols (旅行与网络安全的交汇:正规私人黑客合法联系方式探寻指南与安全实践)
In the digital age, tourism has become inseparable from online services, making cybersecurity a critical concern for travelers. This article explores how the principles outlined in the "正规私人黑客合法联系方式探寻指南:安全途径与注意事项" (Guide to Legal Private Hacker Contact Methods: Safe Pathways and Precautions) can enhance travel safety, while delving into practical applications and real-world scenarios.
Cybersecurity Risks in Modern Tourism (现代旅游业中的网络安全风险)
Travelers today rely heavily on digital tools—from booking platforms to navigation apps—exposing them to risks like public Wi-Fi hacking, phishing scams, and data breaches. For instance, hotel networks often lack encryption, allowing hackers to intercept sensitive information such as credit card details or passport scans. The "正规私人黑客合法联系方式探寻指南" emphasizes that understanding these vulnerabilities is the first step toward protection. Legitimate cybersecurity experts can simulate attacks to identify weaknesses in tourism infrastructure, a practice aligned with ethical hacking principles.
Legal Frameworks for Cybersecurity in Tourism (旅游业网络安全的合法框架)
Governments and organizations increasingly mandate cybersecurity audits for tourism businesses. The "正规私人黑客合法联系方式探寻指南:安全途径与注意事项" highlights that certified professionals, such as those with CISSP or CEH credentials, are essential for compliance. For example, a travel agency might hire ethical hackers to conduct penetration testing on its booking system, ensuring compliance with data protection laws like GDPR. This aligns with the guide's recommendation to verify hacker qualifications through formal certifications and contractual agreements.
Case Study: Restoring Access to Stolen Travel Accounts (案例:旅行账号被盗后的恢复方案)
A common travel-related crisis involves hacked loyalty accounts or stolen flight bookings. Following the "正规私人黑客合法联系方式探寻指南:安全途径与注意事项", victims should avoid unverified "quick-fix" services advertised on social media. Instead, platforms like HackerOne or Bugcrowd connect users with vetted professionals who use legal methods—such as forensic analysis—to recover accounts without violating privacy laws. One documented case involved a traveler regaining access to a hijacked Airbnb account within 48 hours through a certified cybersecurity firm.
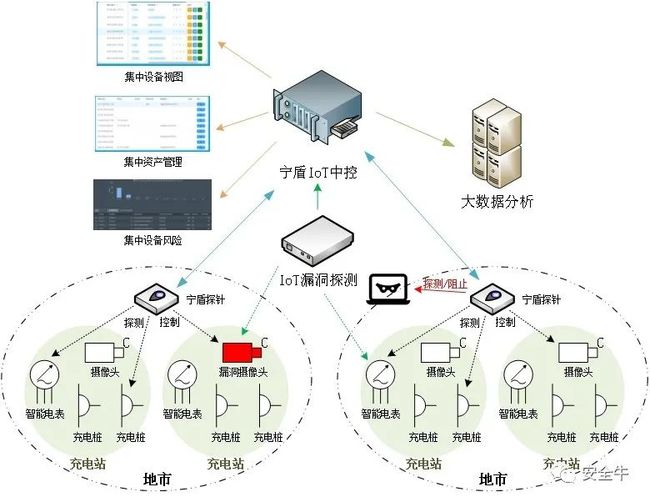
Ethical Hacking for Tourism Infrastructure Protection (旅游基础设施的黑客防护)
Large-scale tourism operators, such as cruise lines or airline alliances, increasingly collaborate with ethical hackers. As per the "正规私人黑客合法联系方式探寻指南", these partnerships require strict non-disclosure agreements (NDAs) and scope-of-work contracts to prevent misuse of vulnerabilities. A notable example includes a European hotel chain that preemptively fixed 17 critical security flaws identified during a controlled hacking simulation, preventing potential data leaks affecting millions of guests.
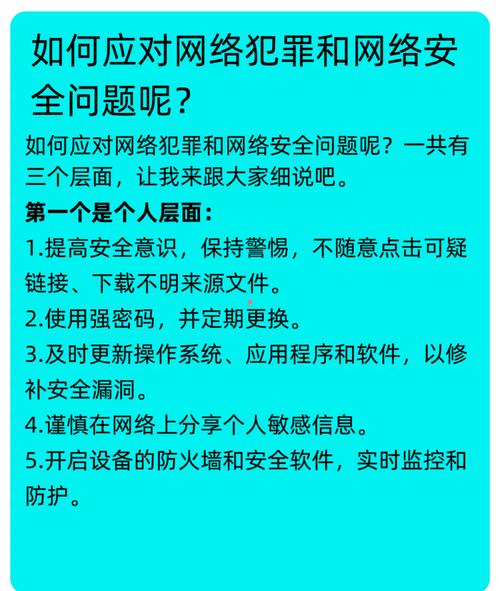
Traveler Education and Proactive Measures (旅行者的安全意识与主动防护)
The "正规私人黑客合法联系方式探寻指南:安全途径与注意事项" stresses individual responsibility. Travelers should learn basic safeguards, such as using VPNs on public networks and enabling multi-factor authentication (MFA) for travel apps. Additionally, the guide advises consulting cybersecurity forums—not for hiring hackers but for understanding emerging threats. For instance, a 2025 report revealed that 34% of airport Wi-Fi hotspots had vulnerabilities exploitable via outdated IoT devices.
Future Trends: AI and Cybersecurity in Smart Tourism (未来趋势:智能旅游中的AI与网络安全)
As AI-powered travel assistants become ubiquitous, so do risks like voice phishing (vishing) attacks. The "正规私人黑客合法联系方式探寻指南" anticipates demand for AI security specialists who can audit neural networks for biases or backdoors. A pilot project in Singapore’s Changi Airport already uses ethical hackers to stress-test AI concierge systems, ensuring they can’t be manipulated to reveal passenger data.
Throughout this exploration, the "正规私人黑客合法联系方式探寻指南:安全途径与注意事项" serves as a foundational resource, demonstrating that cybersecurity is not a barrier to tourism innovation but a necessary enabler. By integrating its principles—legal compliance, professional verification, and proactive risk management—the travel industry can build resilience against evolving digital threats.